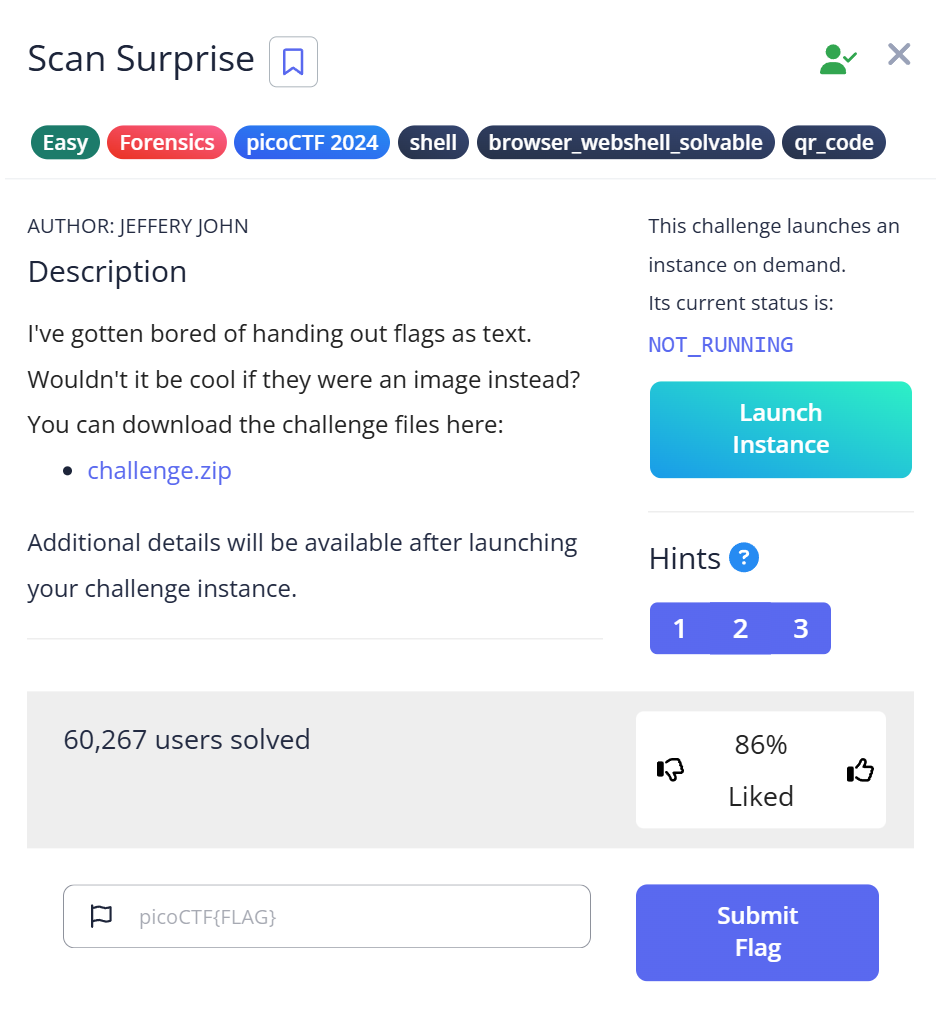
In the world of CTF Forensics, “Easy” doesn’t always mean “Simple.” The Scan Surprise challenge from picoCTF is a perfect example. While most people’s first instinct is to reach for their smartphone to scan a QR code, a pro investigator knows that the command line is faster, safer, and infinitely more scalable.
In this guide, I’ll walk you through my thought process, the “rookie mistakes” I made, and how to master image-based data extraction
1. The Investigator’s Journey: My Trial and Error
Even “Easy” challenges can have friction points. Here is how my actual solve process looked:
| Phase | Action | My “Aha!” (or “Oh no”) Moment | The Takeaway |
| 1. Extraction | unzip challenge.zip | “Why is this buried in so many subdirectories?” | Attackers hide files in deep paths to frustrate manual searches. |
| 2. Inspection | ls and open | “Okay, it’s a QR code. Should I just use my phone?” | Don’t. Using a personal device for CTF files is a security risk (OPSEC). |
| 3. Obstacle | Manual Scan | “The screen glare is making it hard to scan…” | Manual scanning is slow and unreliable for low-res images. |
| 4. Solution | zbarimg | “One command and I have the flag in my terminal. Clean.” | Automation is king. Linux tools remove the human error of manual scanning. |
2. Step-by-Step Walkthrough: Mastering the Workflow
Step 1: Unzipping and “The Deep Dive”
First, we extract the archive.
$ unzip challenge.zip Archive: challenge.zip creating: home/ctf-player/drop-in/ extracting: home/ctf-player/drop-in/flag.png
My Thought Process: Did you notice the path? home/ctf-player/drop-in/. In real forensics, evidence isn’t always sitting on the desktop. Attackers (and CTF creators) often use “Nested Directories” to hide traces. Using unzip immediately tells us the file structure, which is a clue in itself.
Step 2: Identification (Trust, but Verify)
Once you find flag.png, don’t assume it’s a valid image just because of the extension. I always run:

$ file flag.png flag.png: PNG image data, 300 x 300, 8-bit colormap, non-interlaced
Why do this? In harder challenges, a .png might actually be a renamed .zip or a script. Verifying the Magic Bytes via the file command is a habit that will save you hours of frustration later.
Step 3: Decoding with zbarimg
Instead of using a web-based decoder (which could leak your challenge data or be malicious), we use ZBar, an open-source suite for reading bar codes.
$ zbarimg flag.png
QR-Code:picoCTF{p33k_@_b00_3f7cf1ae}
scanned 1 barcode symbols from 1 images in 0 seconds
Success! The flag is revealed instantly in the terminal.
3. Deep Dive: The Tech Behind the QR
Why did this work so well? Let’s look at the Forensics of a QR Code:
- Alignment Patterns: Those three large squares at the corners? They allow
zbarimgto recognize the code even if it’s rotated or distorted. - Error Correction: QR codes use Reed-Solomon error correction. This means even if the
flag.pngwas slightly corrupted or blurry, a forensic tool could likely still reconstruct the data.
Real-World Application
In the “wild,” attackers use QR codes for Quishing (QR Phishing). They replace legitimate QR codes in public places with malicious ones that lead to credential-stealing sites. Forensic analysts use tools like zbarimg to safely extract these URLs in a “sandbox” (like your Linux VM) without ever opening a browser.
4. Troubleshooting: “The Tool Isn’t Working!”
If you tried to follow along and hit a wall, check these two common beginner traps:
- Command Not Found: If your terminal says
zbarimg: command not found, you need to install it. On Ubuntu/Kali, run:sudo apt update && sudo apt install zbar-tools -y - Inverted Colors: Sometimes CTFs provide QR codes with inverted colors (white on black).
zbarimgcan struggle with this. If that happens, usemogrify -negate flag.png(from the ImageMagick suite) to flip the colors back before scanning.
5. Summary & Key Takeaways
| Tool | Purpose | Why it matters for SEO/E-E-A-T |
| unzip | Extraction | Handling nested data structures efficiently. |
| file | Verification | Identifying “File Header” spoofing. |
| zbarimg | Decoding | Secure, automated, and professional-grade analysis. |
The Flag: picoCTF{p33k_@_b00_3f7cf1ae}
Further Reading
Here are related articles from alsavaudomila.com that complement this challenge:
- “RED picoCTF Writeup The Best Way to Reveal Hidden Secrets in Images”Ready to go beyond QR codes? Dive into the world of Steganography. This guide explains advanced techniques to extract hidden data from seemingly ordinary images that traditional scanners might miss.
- “DISKO 1 picoCTF Writeup: How to Analyze .dd.gz Disk Images and Find Hidden Flags”Once you’re comfortable with single files, it’s time for Disk Forensics. Learn the professional workflow for mounting
.dd.gzimages and hunting for evidence buried deep within a file system. - “Corrupted file picoCTF Writeup: How to Use Secret Binary Tactics for Direct Success”Encountering a “file cannot be opened” error is where the real fun begins. In this writeup, I reveal how to use a Hex Editor to manually repair corrupted headers and force the flag to reveal itself.