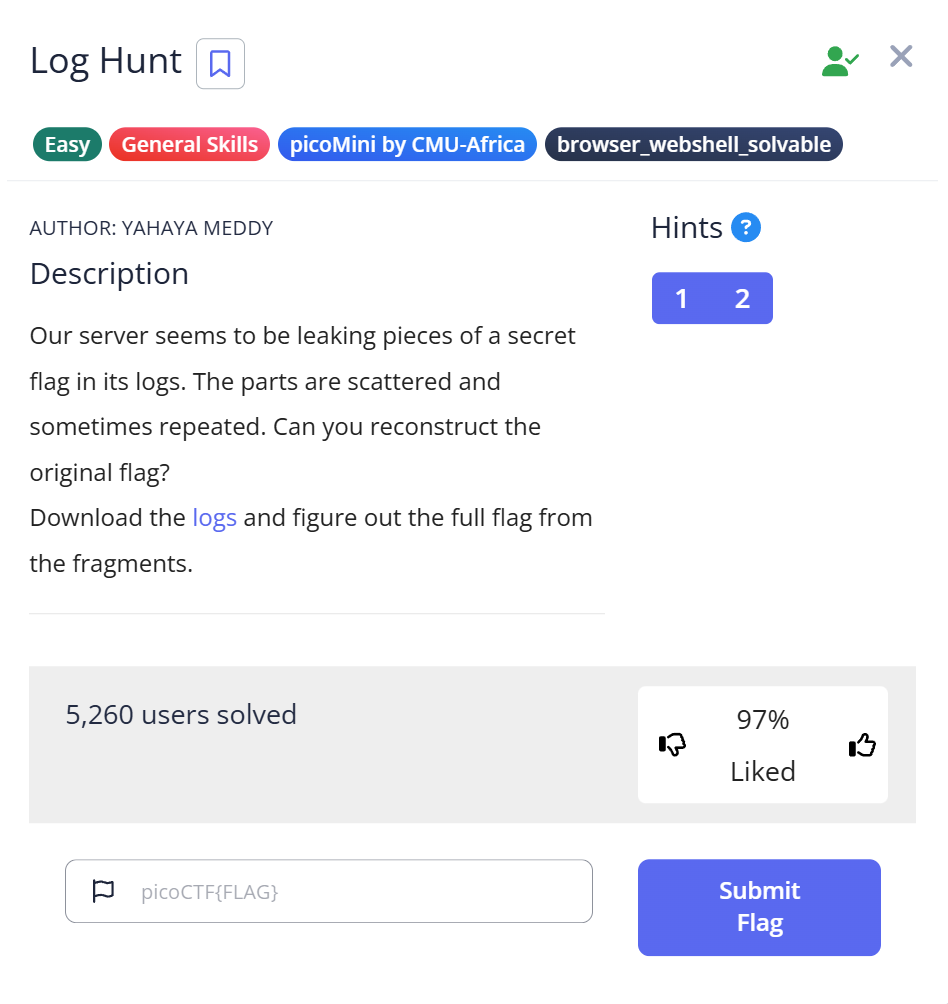
🧩 Challenge Overview
In this challenge, you are given a log file named server.log. By inspecting its contents, you’ll find several pieces of a flag hidden across multiple log entries. Your task is to extract those pieces, piece them together, and reveal the full flag.
This challenge introduces two useful Linux utilities — strings and grep — which are powerful for searching patterns inside text or binary files.
⚙️ Step 1: Check the file type
Let’s start by examining what kind of file we’re dealing with.
$ file server.log server.log: ASCII text
📝 Explanation:
The file command identifies file formats. Since it’s a plain ASCII text file, we can open or search it using common text tools like cat, less, grep, or strings.
🔍 Step 2: Inspect the file content
Open the file or use cat to see what’s inside. You’ll notice lines like:
[1990-08-09 10:00:10] INFO FLAGPART: picoCTF{us3_
This line shows part of a flag beginning with picoCTF{us3_}. However, the complete flag isn’t visible yet.
📝 Explanation:
Log files often contain repeated or partial information over time. If we can identify a pattern (like “FLAGPART”), we can extract only the relevant lines.
🧠 Step 3: Use strings and grep to filter the flag parts
We can extract readable text with strings, then filter lines containing the keyword FLAGPART using grep:
$ strings server.log | grep "FLAGPART"
[1990-08-09 10:00:10] INFO FLAGPART: picoCTF{us3_
[1990-08-09 10:02:55] INFO FLAGPART: y0urlinux_
[1990-08-09 10:05:54] INFO FLAGPART: sk1lls_
[1990-08-09 10:10:54] INFO FLAGPART: cedfa5fb}
...
📝 Explanation:
strings: Extracts readable ASCII text from files (useful even if the file is binary).grep "FLAGPART": Filters the text output, showing only lines that contain “FLAGPART.”
This combination isolates the meaningful parts of the file — the flag fragments.
🧩 Step 4: Reconstruct the full flag
From the extracted parts, we can see the repeated sequences forming the flag:
picoCTF{us3_
y0urlinux_
sk1lls_
cedfa5fb}
Combine them to reconstruct the flag:
picoCTF{us3_y0urlinux_sk1lls_cedfa5fb}
🏁 Capture the Flag
🎉 Flag: picoCTF{us3_y0urlinux_sk1lls_cedfa5fb}
📊 Summary
| Step | Command / Action | Purpose | Key Result |
|---|---|---|---|
| 1 | file server.log | Check the file type | Confirmed it’s ASCII text |
| 2 | Manual inspection | View file content | Found fragments of the flag |
| 3 | strings server.log | grep "FLAGPART" | Extract and filter readable data | Found all flag parts |
| 4 | Combine fragments | Rebuild full flag | picoCTF{us3_y0urlinux_sk1lls_cedfa5fb} |
💡 Beginner Tips
- 🧰 Combine tools like
strings,grep,awk, andcutto quickly extract relevant information from large files. - 🔁 Redundant or repeated log entries can still hold valuable hints — focus on the consistent patterns.
- 🚀 If the file is huge, use
less,head, ortailto preview small sections first. - 📑 When filtering, quote your search term to avoid shell interpretation issues (e.g.,
grep "FLAGPART"notgrep FLAGPART).
🎓 What you learn (takeaways)
- How to analyze log files effectively using Linux commands.
- How to use pipes (
|) to combine multiple tools for streamlined workflows. - How to identify and reconstruct hidden data fragments inside large text files.
- That flags are often spread across multiple lines or logs — look for repeating key patterns.
⚡ Short explanations for commands / techniques used
file <filename>
Detects file type and encoding. Helpful before choosing analysis tools.strings <filename>
Extracts readable text from any file, even binary ones. Essential for CTFs where data may be hidden in non-text formats.grep "PATTERN"
Searches text for specific patterns and prints matching lines. Works perfectly withstrings.|(Pipe)
Sends the output of one command to another. Example:strings file | grep FLAGfilters readable text directly.
Leave a Reply