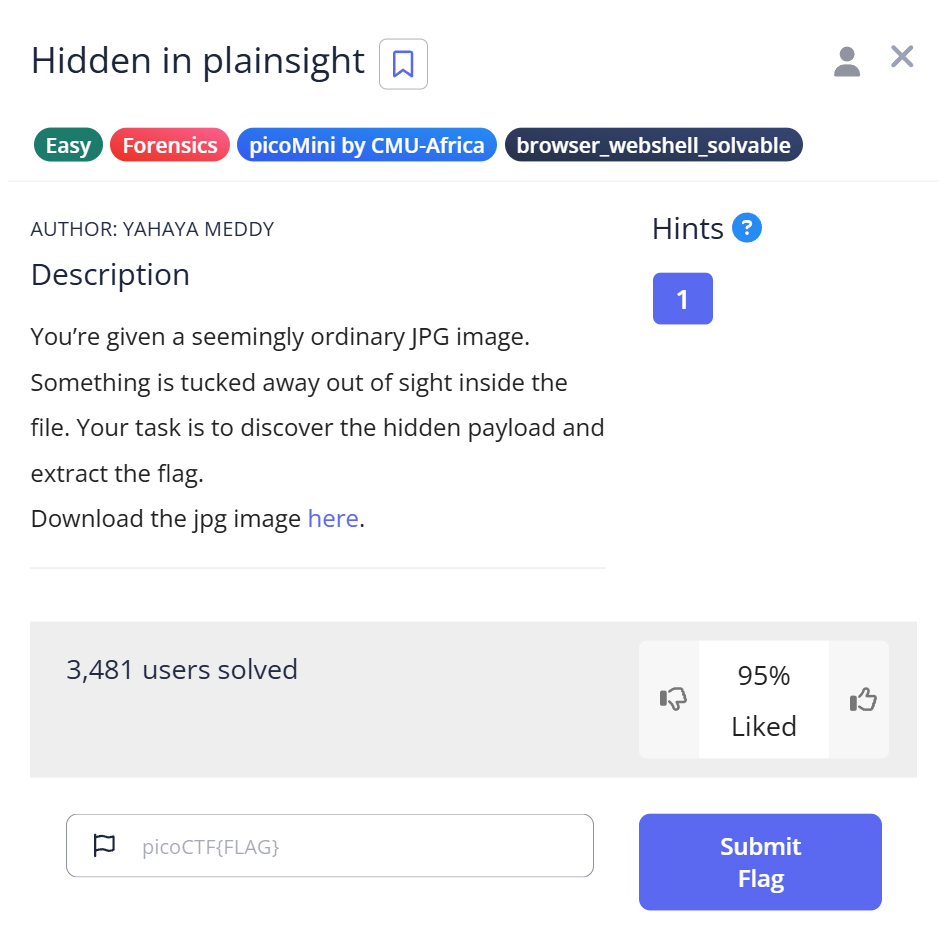
🧩 Challenge Overview
In this challenge, we receive an image file named img.jpg. At first glance, it looks like a normal JPEG, but hidden within it lies secret data — a flag!
This task teaches you how to inspect image metadata, decode Base64-encoded strings, and use a steganography tool called steghide to extract hidden information.
🪄 Step 1: Check the file type and metadata
Start by checking what type of file we are dealing with and whether it contains any hidden information.
$ file img.jpg img.jpg: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, comment: "c3RlZ2hpZGU6Y0VGNmVuZHZjbVE9", baseline, precision 8, 640x640, components 3
We can see a comment field in the image metadata:
comment: "c3RlZ2hpZGU6Y0VGNmVuZHZjbVE9"
This string looks like Base64-encoded data.
📝 Explanation:
The file command not only identifies file types but also shows metadata details for images (like comments). If you notice suspicious encoded strings (letters, numbers, +, /, and =), it’s often Base64 data worth decoding.
🐍 Step 2: Decode the Base64 string
We can use a short Python script to decode it:
import base64 cipher = "c3RlZ2hpZGU6Y0VGNmVuZHZjbVE9" plain = base64.b64decode(cipher).decode() print(plain)
Running this script gives:
$ python3 decode.py steghide:cEF6endvcmQ=
The decoded text reveals another Base64 string after the word “steghide:”.
📝 Explanation:
This tells us the image likely hides data using the tool steghide, and the second encoded string (cEF6endvcmQ=) might be the password for extraction.
🔁 Step 3: Decode again to get the password
We decode the second Base64 string:
import base64 cipher = "cEF6endvcmQ=" plain = base64.b64decode(cipher).decode() print(plain)
Executing it:
$ python3 decode.py pAzzword
We now have a password — pAzzword — to use with steghide.
📝 Explanation:
Base64 encoding can appear in multiple layers. Always check if your decoded result still looks encoded (ends with = or seems unreadable).
🕵️ Step 4: Inspect the image using Steghide
Now, let’s use steghide to check if there’s hidden data inside the image.
$ steghide info img.jpg
"img.jpg":
format: jpeg
capacity: 4.0 KB
Try to get information about embedded data ? (y/n) y
Enter passphrase:
embedded file "flag.txt":
size: 34.0 Byte
encrypted: rijndael-128, cbc
compressed: yes
When prompted for the passphrase, enter pAzzword.
This reveals there is an embedded file named flag.txt.
📝 Explanation:steghide info shows whether hidden content exists. If it asks for a passphrase, you already have a hint that the image has embedded data.
📂 Step 5: Extract the hidden file
Now extract the hidden file using the same password:
$ steghide extract -sf img.jpg Enter passphrase: wrote extracted data to "flag.txt".
After entering pAzzword, a new file flag.txt appears.
📝 Explanation:
The option -sf (stegofile) tells steghide which file to extract from. When successful, it writes the hidden content into a visible file — in this case, flag.txt.
🏁 Capture the Flag
Open flag.txt to find the hidden message:
picoCTF{h1dd3n_1n_1m4g3_67479645}
🎉 Flag: picoCTF{h1dd3n_1n_1m4g3_67479645}
📊 Summary
| Step | Command / Script | Purpose | Key Result |
|---|---|---|---|
| 1 | file img.jpg | Inspect file type and metadata | Found Base64 string in comment |
| 2 | Python base64.b64decode() | Decode first Base64 string | Revealed “steghide:cEF6endvcmQ=” |
| 3 | Python base64.b64decode() again | Decode nested Base64 | Found password pAzzword |
| 4 | steghide info img.jpg | Check for hidden data | Found embedded file flag.txt |
| 5 | steghide extract -sf img.jpg | Extract hidden file | Recovered flag.txt containing flag |
💡 Beginner Tips
- 🧠 Always inspect file metadata — valuable hints often hide there!
- 🧩 If you see text ending with “=” or filled with random letters/numbers, it’s likely Base64.
- 🐍 Use Python’s built-in
base64library for quick decoding. - 🔐 When using steganography tools, remember the password may itself be encoded.
- 🧰 Keep decoding until the result looks meaningful.
🎓 What You Learn (Takeaways)
- How to analyze image metadata using the
filecommand. - How to recognize and decode Base64 strings (sometimes nested).
- How to use steghide to uncover hidden data in images.
- How encoding and encryption can layer data concealment in CTFs.
⚡ Short Explanations for Commands / Techniques Used
file <filename>— Detects file type and shows metadata (for images, includes comment fields).base64.b64decode()— Python function to decode Base64-encoded data back to plain text.steghide info <image>— Checks if the image has embedded content and displays details.steghide extract -sf <image>— Extracts hidden data from the image file.- Base64 Encoding — Represents binary data in ASCII text using
A–Z,a–z,0–9,+,/, and=. Often used for hiding short messages in metadata.
Leave a Reply