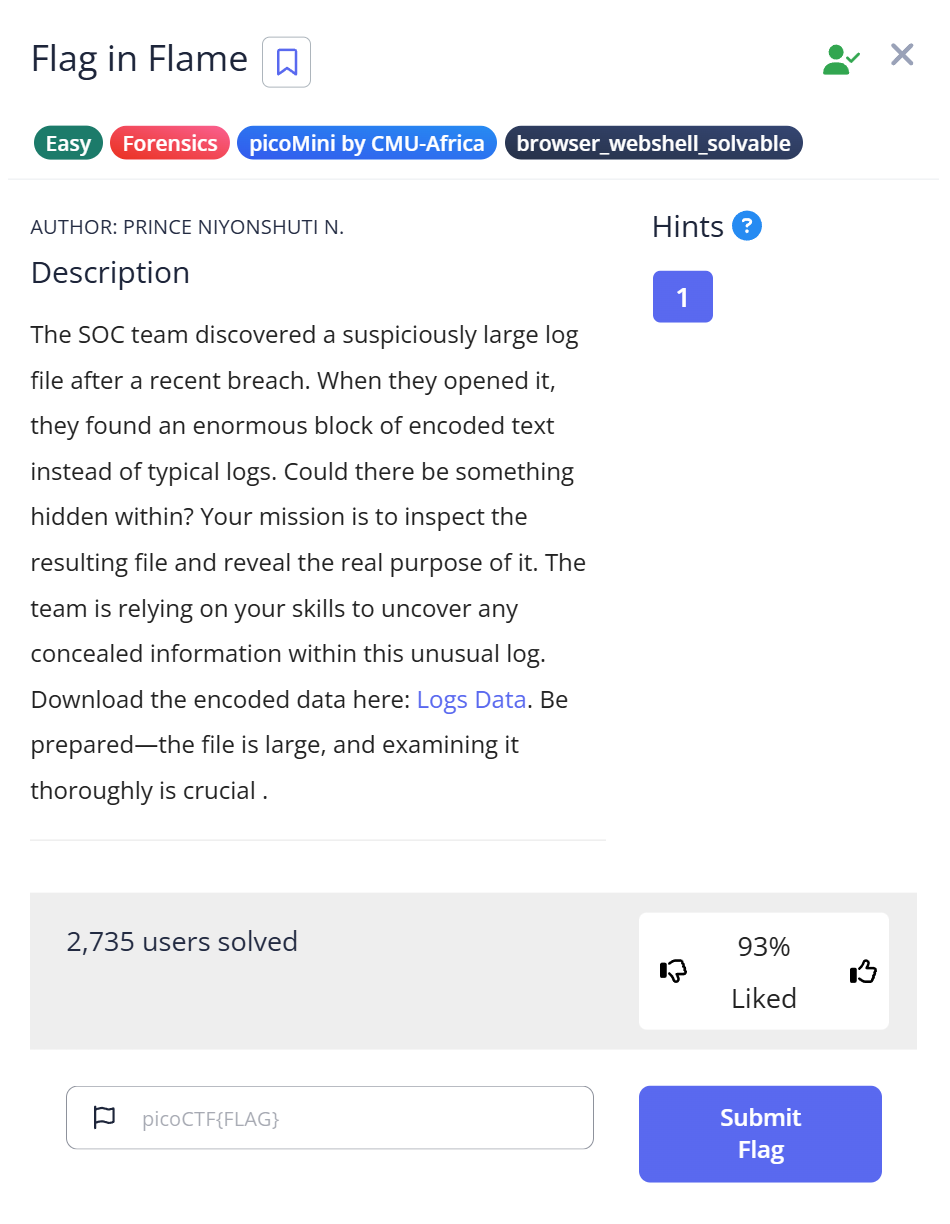
📝 Challenge Overview
You are given a text file (logs.txt) that contains a very long Base64-encoded line. By decoding that Base64 you recover binary data (a PNG). Inspecting the PNG reveals a long hex string embedded in the image; decoding the hex yields the final flag. This is a small forensics pipeline: Base64 → file identification → image → hex → plaintext.
🔎 Step 1: Inspect the downloaded file
- Download
logs.txtand check its type:
$ file logs.txt logs.txt: ASCII text, with very long lines (65536), with no line terminators
- Open or preview the file (it’s one very long line) and notice it looks like Base64 text.
📝 Explanation: file tells you the file is plain text with very long lines. A long line of characters containing A–Z a–z 0–9 + / = strongly suggests Base64 encoding.
🧩 Step 2: Decode Base64 into a binary file
- Decode the Base64 stream and write the binary output to a file:
$ cat logs.txt | base64 -d >> log.dat
(You can also use base64 -d logs.txt > log.dat to overwrite instead of appending.)
- Confirm what you produced:
$ file log.dat log.dat: PNG image data, 896 x 1152, 8-bit/color RGB, non-interlaced
📝 Explanation: Decoding Base64 converts the ASCII encoding back to raw bytes. file shows the decoded bytes form a PNG image, so we should treat log.dat as an image.
🖼️ Step 3: Rename and view the image
- Give the decoded binary a proper extension and open it in an image viewer:
$ cp log.dat log.png # then open log.png in an image viewer or `display log.png`
- Examine the image visually — you’ll find a line(s) of characters (a hex string) embedded in the image.
📝 Explanation: Many tools and viewers use file extension to select handlers; renaming to .png makes it easy to open. The image contains visible data (a hex string) — treat that as the next encoded artifact.
🔐 Step 4: Extract and decode the hex string
- Copy the hex string from the image — e.g.:
7069636F4354467B666F72656E736963735F616E616C797369735F69735F616D617A696E675F61633165333538347D
- Use Python to decode hex → text:
hex_string = "7069636F4354467B666F72656E736963735F616E616C797369735F69735F616D617A696E675F61633165333538347D"
decoded_text = bytes.fromhex(hex_string).decode('utf-8')
print(decoded_text)
- Running the script prints:
picoCTF{forensics_analysis_is_amazing_ac1e3584}
📝 Explanation: The long string is hexadecimal encoding of ASCII bytes. Converting hex to bytes and decoding as UTF-8 reveals the readable flag.
🏁 Capture the Flag
🎉 The decoded flag is:picoCTF{forensics_analysis_is_amazing_ac1e3584}
📊 Summary
| Step | Command / Action | Purpose | Key Result |
|---|---|---|---|
| 1 | file logs.txt | Identify file type and surface clues | Recognized long ASCII lines → likely Base64 |
| 2 | cat logs.txt | base64 -d >> log.dat / base64 -d logs.txt > log.dat | Decode Base64 to raw bytes | Produced log.dat (binary) |
| 3 | file log.dat → cp log.dat log.png → open log.png | Identify and view decoded image | Found embedded hex string inside image |
| 4 | Python bytes.fromhex(...).decode('utf-8') | Convert hex to plaintext | Revealed flag picoCTF{...} |
💡 Beginner Tips
- 🔎 If a text file looks like a jumble of
A–Z a–z 0–9 + / =, think Base64. - 🧾 Prefer
base64 -d infile > outfileto avoid accidental appends when re-running commands. - 🖼 If
filereports an image, rename the decoded binary with the proper extension (.png,.jpg) and open it. - ✂️ When copying long strings from images, watch for line breaks or OCR errors — use a text editor to paste and verify.
- 🐍 Use small Python snippets for quick binary/hex/string decoding — they’re unambiguous and scriptable.
🎓 What you learn (takeaways)
- How to chain simple forensics steps: detect encoding → decode Base64 → identify file type → view artifact → decode contained data.
file,base64, and small Python utilities are powerful together for recovering hidden data.- Encodings often appear in layers (Base64 containing an image that contains hex), so keep decoding until you reach plaintext.
⚡ Short explanations for commands / techniques used
file <filename>— Detects file type and gives hints (text, image, hexdump, etc.). Use it first to choose the right tools.base64 -d/cat file | base64 -d— Decodes Base64 text into raw bytes. Use>to write or>>to append cautiously.- Renaming binary →
.png— Makes it easy to open the decoded bytes in an image viewer; extension helps tools pick the correct handler. bytes.fromhex(...).decode('utf-8')(Python) — Converts a hex string into bytes then to readable text; ideal for decoding hex-encoded ASCII.- Image inspection — Visual inspection (open image) often reveals embedded text/artifacts that are themselves encoded.
Leave a Reply